Our daily work can't be done without documents and files. And there will be no data safety for document/files without password. While, where there is password, there is password forgotten/lost. So you need to recover the password. The thing you need to know is that it will be very difficult even impossible to recover password without password recovery programs. However, many people spent hours, days, even longer time while using password recovery programs to find a lost password. It's because they didn't pick the right way.
Now, this article will show you how to set different kinds of parameters for password recovery attack type: Brute-force, Mask, and Dictionary with iSumsoft password refixer program – Office/RAR/ZIP/PDF Password Refixer. The purpose of this tutorial is to help speed up the password recovery process.
Dictionary Attack means you save all the possible passwords in a text file, then the password recovery program will look for the password from the text file (dictionary) one by one until it finds your password. In this way, you won't need to manually type the passwords one by one to try to open the password protected document/file.
When you choose Dictionary attack type, password recovery program will try all the passwords strings in its built-in or yourself-created dictionary. If the password is in the self-created password dictionary, this program can identify it rapidly. So how to create a powerful password dictionary file?
To create an additional custom dictionary, follow these steps:
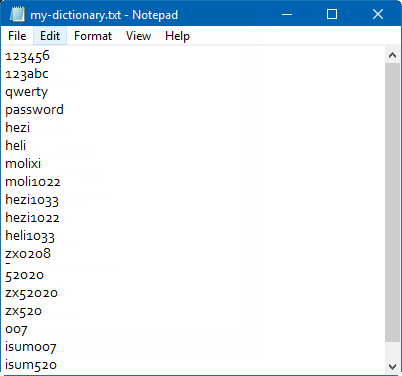
1. Start a Notepad on your computer.
2. Type into all possible passwords, every combination of characters, digits and symbols, a password in a line.
3. When done, save it, and type a name for the new custom dictionary if you like.
The following quick tips will help you create a more powerful dictionary.
1. Most commonly used passwords.
People continue to use easy-to-guess passwords to protect their information. For example, "123456", "password", "1234567890", "abc123", "qwerty" and "iloveyou".
2. The passwords you have ever used.
3. Some special character strings.
Such as your birthday, name, name + birthday, phone number, doorplate number, some special dates, the pet's name. And this information of your family members can be used for dictionary attack.
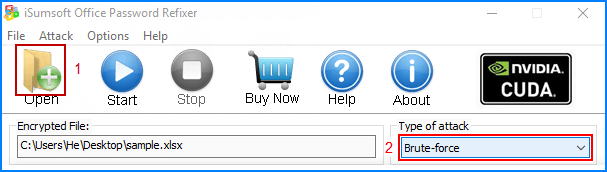
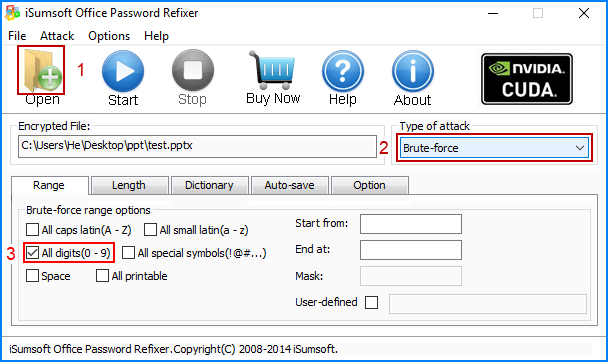
Step 1: Download and install the Office Password Recovery Refixer, then run it.
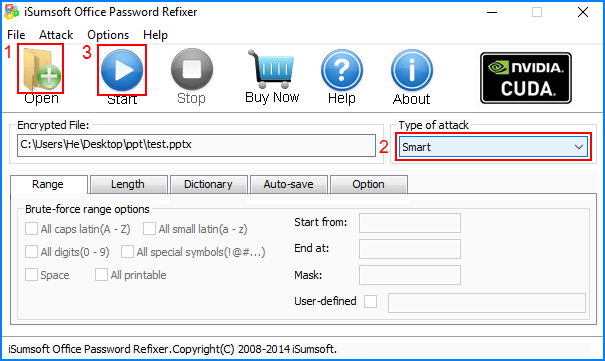
Step 2: In the password recovery program, click on the "Open to import your encrypted file. Select Dictionary attack.
Step 3: Click "Dictionary" tab, and then click "Select Dictionary", and then choose the dictionary file you have created.
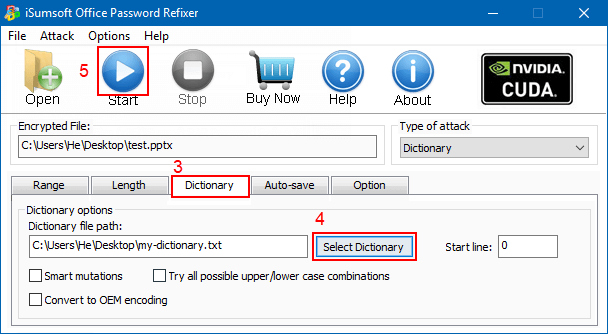
Step 4: Click Start button to start the password recovery process. If the protected password is in the self-created password dictionary, this program will quickly get it and your correct password will be displayed in a popup window.
Mask is also called Brute-force with Mask, so it can be set based on Brute-force settings. For example, some options in Range can be set like Brute-force, such as characters type, Start from, End at option.
If you can recall a part of the password, such as password length, character, number and so on, you can choose this attack type and customize the range, length and Mask to shorten the password recovery time (Highly recommend). Otherwise, Brute-force attack has been effective enough to recover password. This program will crack password according to your settings.
What password features do you know?
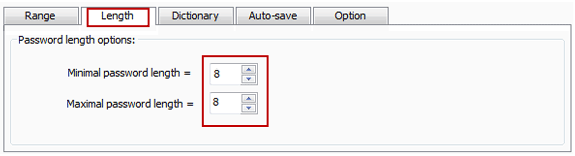
1. Password length.
If you know exactly how many numbers in the passcode, or presumably know how many numbers in the password, then please be sure to set the password length. For example, if you know the password length is 8, please set both the Minimal password length and Maximal password length to 8.
2. Know some parts of the password.
For example, you know the first few characters or the last few characters of the password.
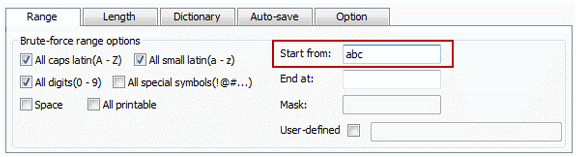
2-1. If you know first three characters are "abc", but have no idea the rest one, then just enter "abc" in the Start from box.
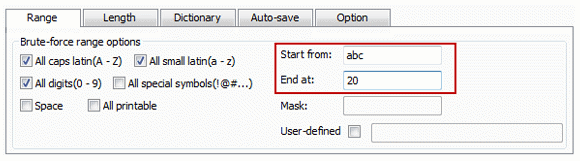
2-2. If you know the password's first three characters are "abc", the last two characters are "20" and have no idea the middle part, then you can put abc in the Start from box and put 20 in the End at box.
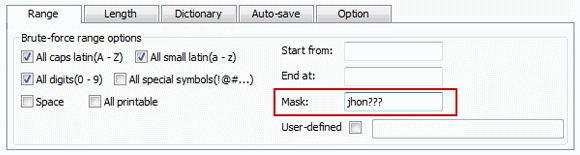
2-3. If you know the password is eight characters long and the first four characters are "jhon", then you can set the minimal password length and maximal password length are 8. And set the Mask as "jhon????". So the password recovery program will help you quickly find the four remaining characters.
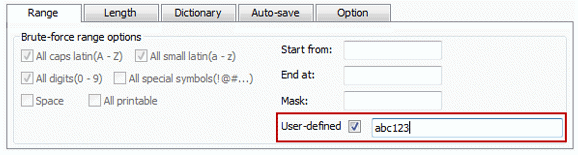
3. Know exactly what characters the password consists of, but have no idea the sequence of the characters. For example, you can remember your password consists of "abc123" but have no idea the exact sequence, and have no idea the total number of the characters, then you can check the User-defined and write "abc123" in the box. Then the password recovery program will find your password from the defined characters.
4. Know what characters the password contains and doesn't contain.
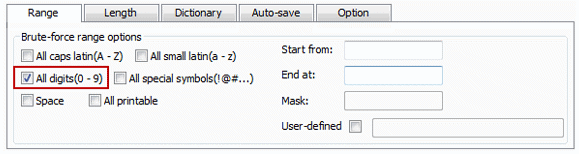
If you know the password only contains digits, please check All-digits(0~9) and uncheck the other character set options.
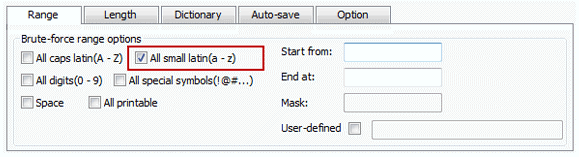
If the password only contains lowercase letters, then check All small latin(a~z) and uncheck the other options.
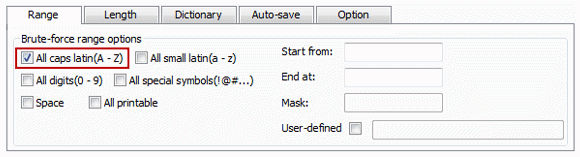
If the password only consists of capital letters, then check All caps latin and uncheck the other options.
Tips: Both the above two password recovery methods are imposed on local passwords for Office/RAR/ZIP/PDF/iTunes documents/files.
Brute-force is a commonly-used password recovery attack type.
When you choose Brute-force, this program will search every possible combination of characters. Length and Range are two features which could largely improve password recovery speed. If you remember the password just contain digits, you only need to select all digits, you also can set the minimal and maximal length of password. The more accurate settings you made, the faster you can recover the password. If you remember the beginning and/or ending parts of the password, you can select Mask attack.
How to set the range options?
If you know what characters your password probably consists of, and check box of All caps latin(A-Z), All small latin(a-z), All digits, All special symbols, Space(blank key), or All printable. For example, if you remember the password consists of digits only, then check All digits(0-9) option, and uncheck the others options.
If you select this attack, all range and length settings are set by default. Our password program will try all possible character combinations until finding the right password. Simply choose Smart attack from the pull-down list and click Start button to start cracking. It will be performed to find out your password but that is the most time-consuming approach.
1. If you have a self-created dictionary file which may contain the password, please use it. This can recover the password easier than any other attacks.
2. If you remember part of symbols of your password still, it's highly recommended to use Mask attack, which can perform a fast computational and recovery speed. Otherwise, it's quite smart for you to choose Smart Attack at first. There are no settings on this attack. If you don't know any parts of the password, select Brute-force or Smart.
3. The difference between Brute-force and Smart is that you can set the range options under Brute-force, but you can't set anything except for the length of the password under Smart.
1. Online password
An online password is a password which is encrypted and stored in the remoter server. Your entered password will be transmitted to the remote server through the Internet. After comparison, the server will return the results whether your entered password is correct or not. For example, the common online passwords are Google accounts passwords, apple accounts passwords, facebook accounts passwords, your bank card password .etc.
2. Local password
The local password means that the encrypted password will be stored on your computer, mobile or other local devices. When you enter the password, the password recovery program will compare your entered password to the local password and then give the results whether your entered password is correct or not. The clear difference between the online password and local password is that the former requires network transmission and the latter doesn't require any network transmission.