This page shows the specific steps to use iSumsoft Office Password Refixer software to retrieve lost/forgotten passwords for Microsoft Office document including Word document, Excel Workbook, Presentation, and so forth.
What do you need?
Software: iSumsoft Office Password Refixer.
OS Support: Windows NT4/2000/XP/2003/Vista/2008/2012/2016, Windows 7/8/10.
Hardware Requirements: 100 MB or more; 256 MB or above.
1. Get Office Password Refixer software and install it on your computer. After the installation is complete, launch the software. Click the Open button.
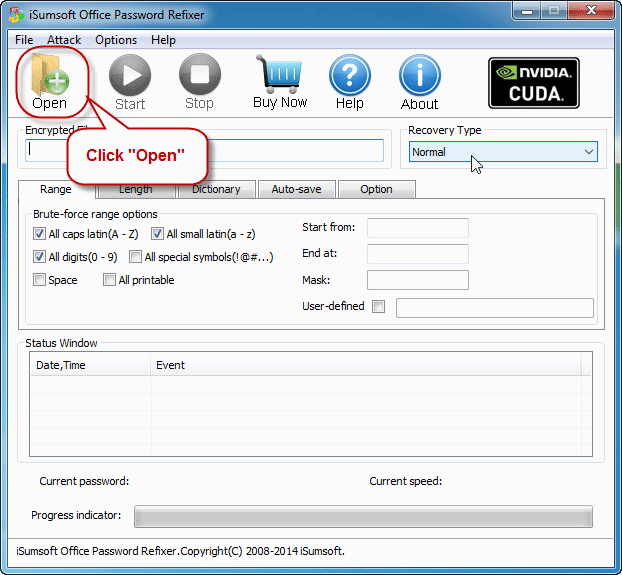
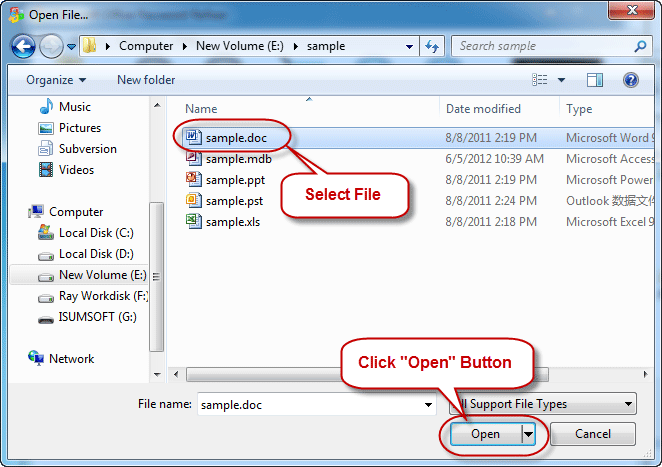
2. In the Open File dialog, navigate to the path to the password-encrypted Office document; it can be a Word/Excel/PowerPoint document, an Outlook .pst file, or an Access .mdb file. Then select the target file and click Open to import it into the Office Password Refixer software.
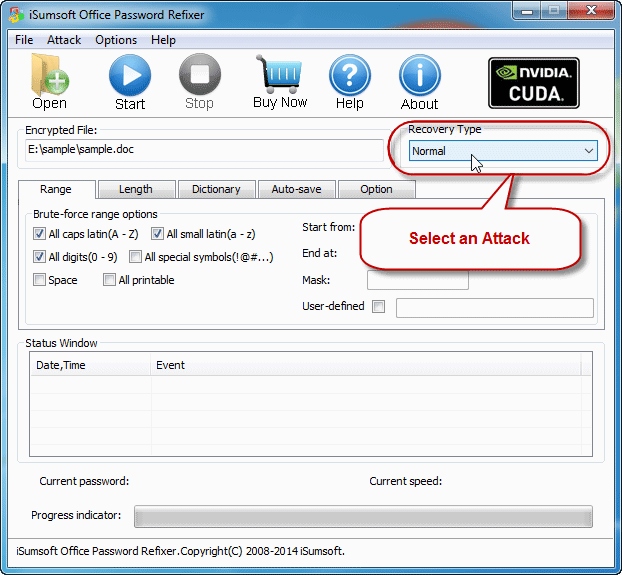
Select one of the password recovery types (Normal, Mask, Dictionary, and Smart), and make the relevant settings as needed.
Tips: See Dictionary and Mask mode to help you make a better choice. What's more, you can refer to How to perform a high performance password recovery with software to help configure the settings and shorten the recovery time.
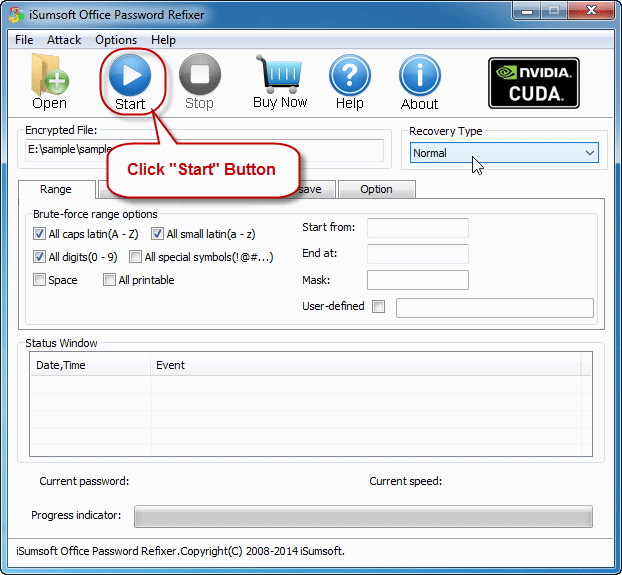
1. Click on "Start".
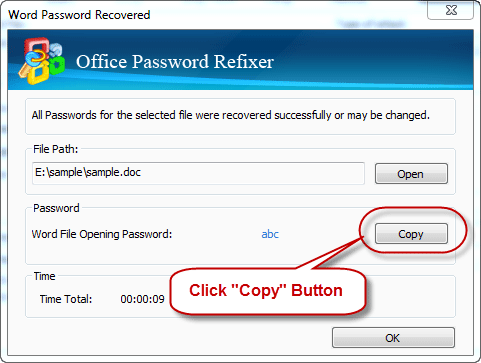
2. Wait for a while till the password is recovered and displayed successfully. Then you can click the "Copy" button and paste the password to open the password-encrypted Office document.
Normal type: Select this attack type if you know little about the Office document password. This attack will try all possible password combinations to find lost password.
Smart type: Select this type if you know nothing about the document password. It will try all possible characters combinations including all printable characters to find the password smartly.